Cut Through The Noise. Respond To Phishing Threats Faster
Around-the-clock autonomous alert investigation enables analysts to detect and neutralize phishing threats more efficiently.
Catch the phish,everytime
Adaptive AI continuously learns and improves to keep up with the evolving threat landscape and correctly distinguish between genuine emails and phishing attempts.
With a conclusive outcome, analysts can stay focused on the most critical alerts.
Conclusive investigations and personalized recommendations help analysts isolate attacks and improve defenses, faster.
Insights from email security and CTI tools are combined to maximize ROI and fortify defenses.
End-to-end investigations in minutes, not hours
As soon as your SIEM/EDR tool triggers an alert about a potential phishing attack, Qevlar AI gets to work. Within 90 seconds, the investigation is complete and:
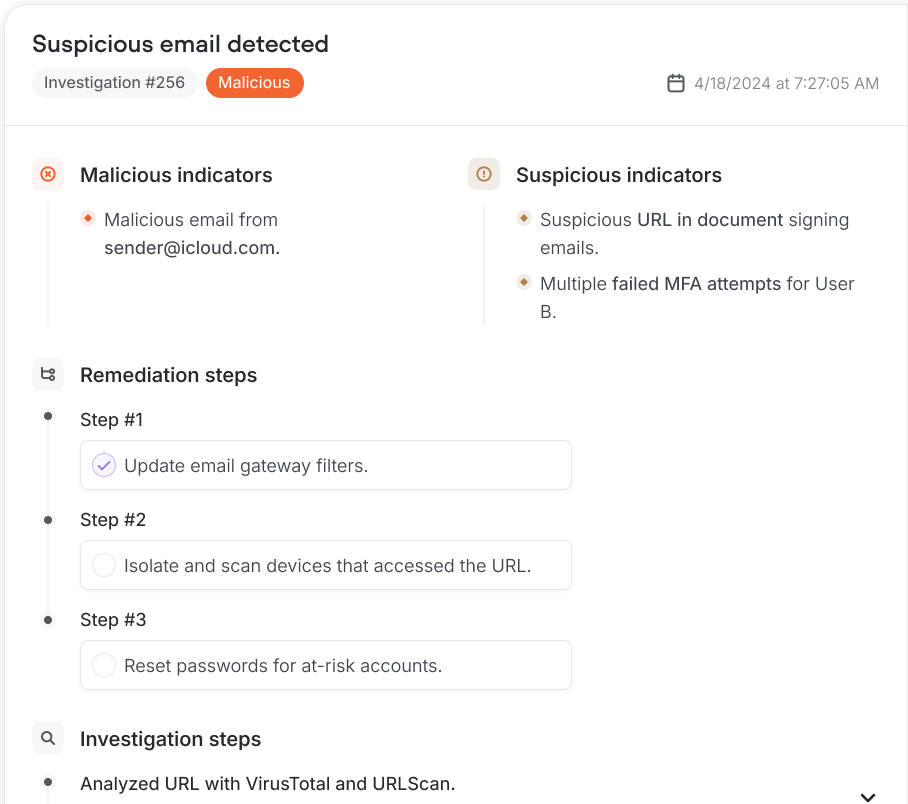
- The alert is conclusively determined to be malicious or not harmful
- A comprehensive incident report is generated
- Recommended remedial actions are suggested










Get a holistic view of the attack
Accurately detect event the most sophisticated attacks with data automatically pulled, enriched, and analyzed from:
Integrate
anything
Minimize risk with swift remediation
Comprehensive but easy-to-read incident reports summarize the outcome of the investigation, outline the data sources that were analyzed, and offer truly actionable next steps.