
Security That Gets Stronger With Each Alert
Qevlar AI transforms your SOC's daily activity into a self-improving defense system that continuously sharpens investigation, detection, response, threat hunting, and vulnerability prioritization












Security teams are flooded with signals but operate in silos.Attackers exploit the gaps.
Most security teams act like firefighters, investigating individual alerts, but their defenses don’t get stronger. The problem is that knowledge disappears when tickets close, analysts leave, and teams work in silos.
Qevlar closes the loop and makes your defenses stronger with each action
Investigations, response, threat hunting, detection engineering, and vulnerability management powered by contextual intelligence that compounds with every action.
Investigates and responds across your stack
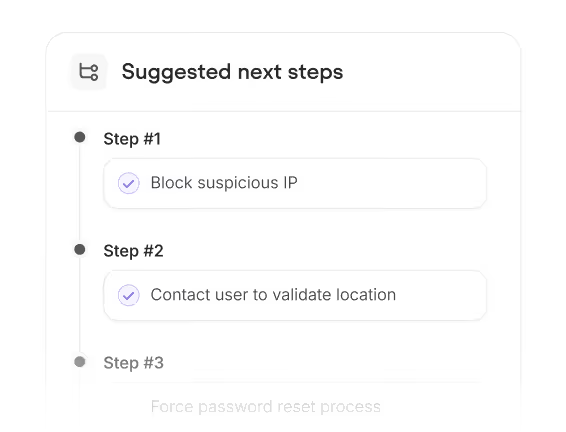
Qevlar investigates every alert across your stack, connects related activity into a single incident story, maps the full blast radius and moves containment forward, following your procedures, with analyst control.
Closes the loop on every incident
Qevlar drives the next action: containment for malicious activity, tuning for false positives, and policy or compliance follow-up for benign violations. So every outcome improves your defences.

Hunts threats continuously
Autonomous hunting for emerging threats, attacker TTPs, behavioural anomalies, active exploitation, and patterns hidden across past investigations. Every finding becomes action. Every gap becomes a chance to strengthen detection.
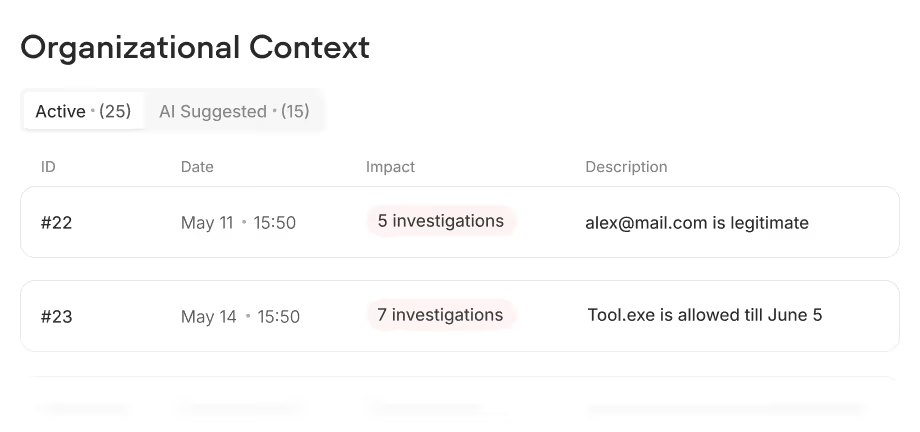
Compounds institutional knowledge
Qevlar adapts to your environment, making investigations faster, decisions more consistent, and the entire SOC smarter with every cycle, regardless of analyst turnover.
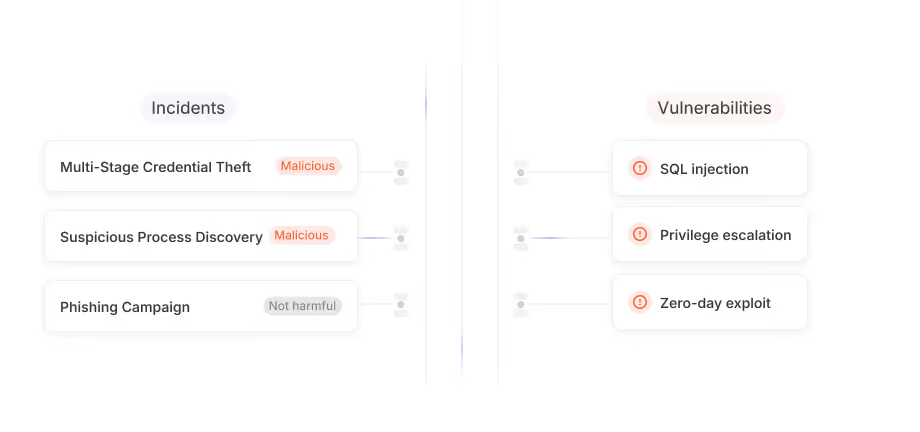
Connects SOC and vulnerability teams
A shared intelligence layer for prioritising real risk. Confirmed exploitation elevates vulnerable assets in the remediation queue immediately, and critical exposures on high-value systems become new hunt priorities for the SOC.


Security That Compounds
Every alert makes your defenses stronger. Detections improve. Coverage expands. Threats get prioritized. Faster and more intelligently each time.
Every investigation and hunt make the next one sharper. Knowledge stays in the platform, and becomes a shared intelligence across security teams.
Your SOPs and policies apply consistently across alerts,workflows, and shifts. Your security strategy becomes your operational reality.
Repetitive operational work handled. Every function in sync. Your team does more, focusing on decisions that matter most.
Qevlar worksin your environment
Connect your tech stack to Qevlar AI via API in minutes. See results directly in your console or ours.

.svg.png)


















%2525202.webp)
.avif)



.avif)





.png)


















.avif)
%2525202.webp)




.avif)






.png)
.svg.png)


















Qevlar AI enhances Almond CWATCH SOC’s ongoing optimization, joining Almond’s ecosystem of SOAR, SIEM, XDR, and its platforms ITERA (managed-as-code detection) and M&NTIS (attack simulation and cyber defense).

“Qevlar was first deployed to enhance our email security investigations. Its impact was immediate and measurable, leading us to expand it across our entire security perimeter.”
“We can now detect threats more quickly and accurately, while focusing our analysts' expertise on the most complex and critical incidents.”

“The integration of Qevlar's autonomous, adaptive agentic AI with Atos cybersecurity delivers incremental operational excellence to protect customer business.”

The business case was easy to validate due to the immediate ROI. We not only reduced operational costs significantly but also improved our operational security efficiency and excellence.

With Qevlar AI, our SOC analysts are now “augmented analysts”, capable of accelerating response times while maintaining quality. This partnership equips us to better protect our clients against evolving cyber threats.
Award-winning technologyfor modern SOCs
Proven in real SOC environments. Recognized by the cybersecurity industry.






Everything you needto become a top-performing SOC

How to detect incidents in an avalanche of alerts: a real case
Qevlar AI Introduces AI Agents Unifying SOC and Vulnerability Operations
Top 3 AI SOC Solutions in 2026: Which One Fits Your SOC?
Want to make the attackers life a bit harder?
Frequently asked questions
How SOC analysts can build trust in Qevlar AI ?


Every verdict is fully transparent: analysts see every step, every observable queried, and the exact reasoning behind the conclusion — nothing is a black box.
Under the hood, Qevlar uses graph-based orchestration, so the same alert is investigated with the same rigor every time.
Analysts can also override any verdict and add context, and Qevlar applies it to future cases.
How Qevlar AI is different from SOARs?


SOAR executes the static playbooks you've already written — and breaks every time your environment or threats change.
Qevlar AI does the investigative thinking: it enriches, pivots across your stack, correlates alerts into incidents, and adapts its path based on what it finds, with no playbook to maintain.
More on this: https://www.qevlar.com/post/qevlar-ai-and-soar-different-roles-one-mission
How Qevlar AI is different from other AI SOC agents or platforms?


Most AI SOC tools stop at alert-by-alert triage. Qevlar AI closes the loop across investigation, response, threat hunting, detection engineering, and vulnerability management, correlating alerts into full incidents, building environment-specific intelligence that compounds over time, and bridging your SOC and vulnerability teams on one live picture.
How Qevlar AI avoids LLM hallucinations?


Qevlar doesn't let an LLM run the investigation. The core is a graph orchestrator — reasoning and decision paths are structured and reproducible — with LLMs used only for narrow, bounded tasks like enrichment and summarisation.
Don’t miss the chance to discover our new capabilities

Vereinbaren Sie jetzt ein persönliches Gespräch an unserem Stand Nr. 4 und erhalten Sie eine exklusive Vorschau unserer neuen Features für Ihr SOC.




















