Shatter barriers between SOC and Vulnerability teams
New AI agents in preview today, generally available this fall.













Problem overview
~30% of the vulnerabilities that go on to be exploited are Zero days: organisations can’t anticipate where and how the next attack will take place. AI models like Claude Mythos are making it easier to identify and exploit zero days, with the average exploitation time expected to drop below 1 day.
SOC and Vulnerability teams hold complementary signals but have no shared workflow or data layer to exchange them. Since incident response and vulnerability management are usually separate functions at an organisation, their teams tend to operate in siloes, resulting in ad hoc collaboration and messy shared workflows and processes.
Current tools enable high volume business as usual VM processes and activities such as patch management. There’s a tooling gap for the early identification, investigation and response to Zero day vulnerabilities, a process that needs input from both SOC and VM teams. Current tools serve the needs of either the SOC or Vuln teams, but no solutions exist that bring both teams together.
Stop Prioritising in Parallel
Security functions depend on effective prioritisation in order to scale their limited resources. However, there’s limited exchange of data between functions which can serve as prioritisation inputs. Qevlar enables more effective prioritization by connecting SOC and vulnerability data so that each team is using the very latest and relevant prioritisation inputs.
- Contextual severity score blends CVE intelligence with live signal from active SOC investigations.



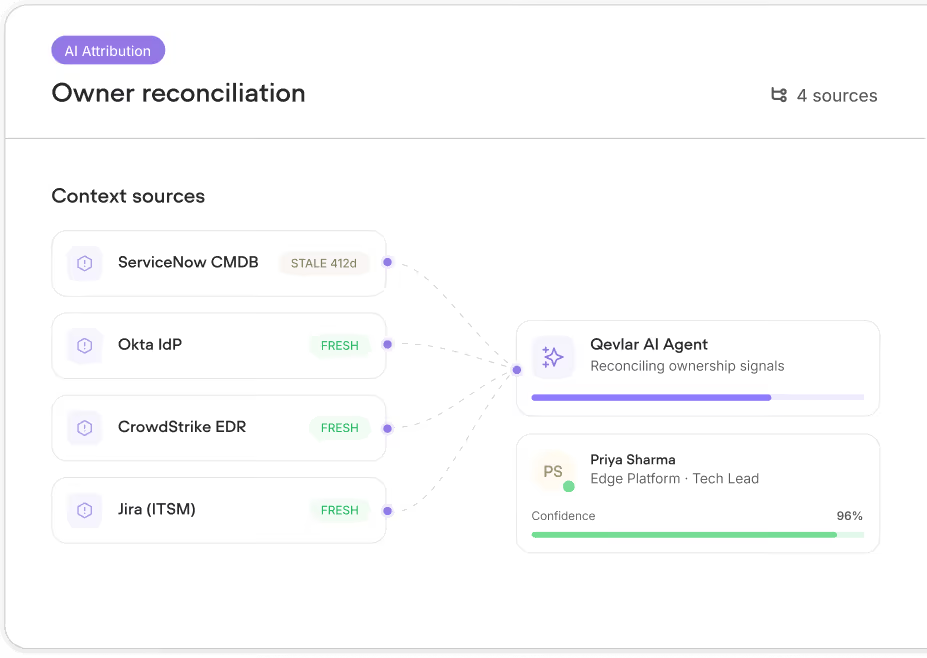
You can’t fix and investigate issues without knowing who’s responsible
Asset ownership records are often out of date or incomplete in CMDBs, but both Vulnerability and SOC teams rely on accurate and maintained asset ownership records in order to address an issue’s root cause. Qevlar automatically identifies an asset’s owner using AI Agents that correlates ownership records from a variety of data and context sources such as ITSMs, Identity Providers and EDR.
- Multi-source reconciliation from CMDB, EDR, IdP, and ITSM.
Patch Tuesday is dead, your vulnerabilities can’t wait to be fixed
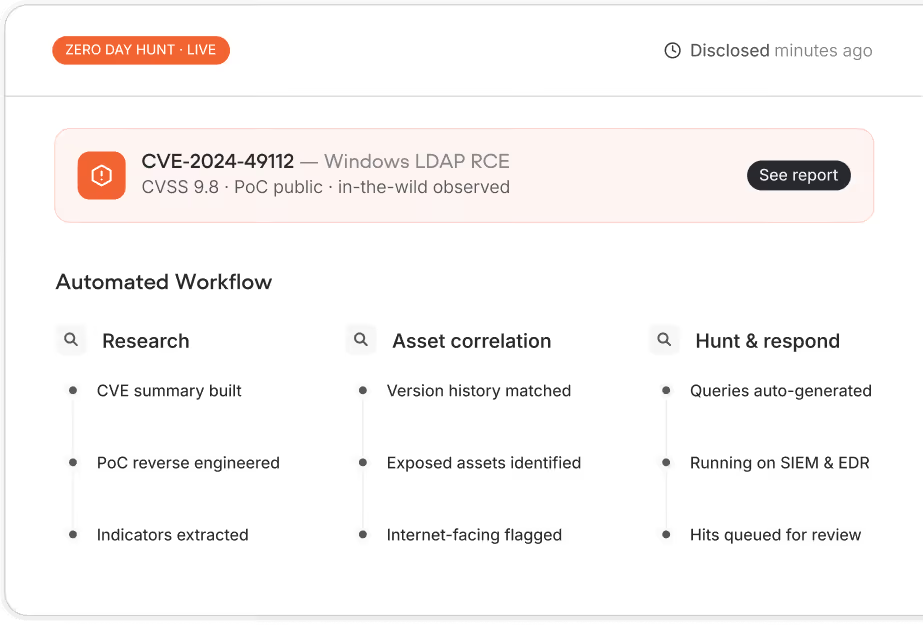
When a zero day vulnerability is published, Vulnerability teams want to get ahead of any impact by identifying where the vulnerability exists and initiate emergency patching protocols. However, they’re left waiting in the dark whilst waiting for their next scan findings to come in, all the while the zero day remains exploitable by attackers. Qevlar mitigates the zero day exploitation problem head on by using AI Agents that automate time consuming and manually intensive vulnerability research and threat hunting
- Threat hunt queries generated and executed across SIEM and EDR automatically.




Outcomes
AI agents start the hunt at CVE disclosure, not after the next scan window.
One signal across SOC and Vulnerability: no handoff friction, no lost context.
AI agents absorb the manual research, ownership-chasing, and triage that grew faster than your team.
Both teams act on the latest SOC and vulnerability signal, against the same clock.










